About Us
Why platform blocking is a weak cybersecurity strategy
- Art Samaniego
- PHT
- Tumblr
DECODED: TECH, TRUTH, AND THREATS
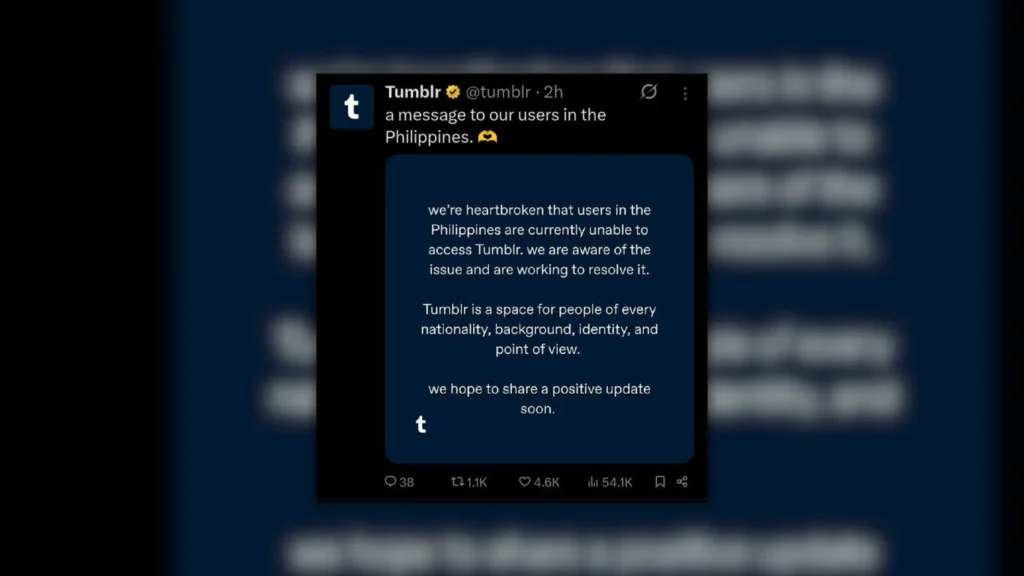
The recent move to block access to Tumblr in the Philippines once again highlights the country’s long-standing digital policy problems. Platform blocking is often presented as a strong response to online threats, yet in practice, it tends to be one of the weakest tools available to address cybercrime.
Early user reports suggest the access issue may not be consistent across all networks. Some users report difficulty accessing the site with one internet provider, while those using other major Philippine networks, such as DITO, Globe, and Smart/PLDT, appear able to reach the platform without difficulty.
If that observation holds true, it suggests the restriction may be implemented unevenly at the service provider level rather than as a consistent nationwide block.
This inconsistency demonstrates why platform blocking is a limited tool.
Most platform blocking implemented by internet service providers relies on relatively basic filtering mechanisms. In many cases, the restriction occurs at the domain name system level, where an internet provider prevents its DNS servers from resolving a domain name to an IP address. Other systems may attempt to block specific IP addresses or filter traffic that contains certain domain names.
These techniques may disrupt access for ordinary users who rely on their devices’ default settings; however, individuals who understand how internet infrastructure works quickly recognize these measures as relatively shallow controls.
Cybercriminals, organized scam networks, and other malicious actors do not depend on a single platform, website, or domain name. Their operations are built around a flexible infrastructure that can move across servers, mirror sites, and multiple hosting providers spread across different jurisdictions. Domains can be changed quickly. New servers can be deployed in hours. Entire platforms can be replicated under different addresses.
By the time a domain is blocked, the activity has often already moved elsewhere.
This creates a familiar pattern. The people most affected by the block are ordinary users who may simply want to access a legitimate platform. Meanwhile, individuals who engage in illegal activity usually possess the technical knowledge needed to continue operating.
From a cybersecurity perspective, blocking platforms rarely addresses the root problem.
Cybercrime operations are not defined by a single platform or website. They are defined by networks of operators, payment systems, infrastructure providers, and coordinated online activity. Removing access to one address does little to dismantle that ecosystem.
The decision to rely on website blocking also raises a more troubling question about institutional capability. When authorities choose this route as a primary response, it suggests an admission that the Department of Information and Communications Technology’s current leadership lacks the technical capability to confront complex cyber threats directly. Instead of developing deeper investigative tools and technical expertise, the easier path is taken, implementing a visible restriction that appears decisive but does little to solve the underlying problem.
In other words, it is a shortcut. It may create the impression of action. It may generate headlines. But in reality, it reflects a weak cybersecurity strategy.
As a cybersecurity professional, I view simple platform blocking as a limited and often symbolic measure. It may demonstrate that authorities are taking action, but it does not necessarily reduce the capability of criminal organizations operating online.
More effective approaches tend to focus on deeper investigative capabilities. Digital forensics, intelligence gathering, financial tracking, and international cooperation are far more powerful tools for addressing organized cybercrime. These methods target the operators behind the activity rather than the visible domains they happen to use at a given moment.
Public awareness also remains one of the strongest defenses. Educating users about scams, phishing, malicious applications, and fraudulent platforms helps reduce the number of victims. Without victims, many cybercrime operations simply cannot survive.
In the end, cybersecurity is not achieved solely by blocking platforms.
Policymakers and cybersecurity professionals should invest in strengthening investigative capabilities, foster international partnerships, and prioritize public education on digital security. By focusing on dismantling cybercrime networks and empowering users with knowledge, institutions can move beyond website and platform blocking to establish more resilient defenses against online threats.
Rather than relying on platform blocking, we must urge the DICT to prioritize long-term strategies grounded in decisive investigation, skilled personnel, and sustained public outreach. This shift is crucial to address cyber threats effectively while minimizing unnecessary burdens on ordinary users.
